
Social Engineering
The biggest initial security threat to your systems are the people using them. We expose human-related risks to help you instill a positive and thriving security culture, where genuine social engineering attacks can be more easily identified.
The benefits of social engineering testing and attack simulation
Social engineering attacks often exploit common human traits, such as curiosity, fear or the desire to help others, so as a result can be challenging to detect. But, with our experience, it’s a challenge we can help you overcome.
Through regular and realistic social engineering testing services and attack simulations, we’re able to guide and educate your people in best practice, so they’re prepared to defend against genuine social engineering attacks.
- Assess your human risks
- Shape policies and procedures
- Educate your workforce
- Drive awareness
- Inspire a positive security culture
- Regular testing to maintain security

The weakest link in your security
Targeting your workforce via social engineering is often the first step a threat actor will take when looking to breach your security, whether via a phishing email, impersonation attack, curated pretexting or social media mining.
Ensuring your people are ready and capable of recognizing a social engineering attack will prevent them from revealing confidential information, installing malware or granting unauthorized access to a system.

SHEEP in a wolf’s clothing
Too few organizations value their teams’ proficiency in detecting psychological manipulation, deception and impersonation. These are the techniques employed by our team of ethical hackers to imitate genuine bad actors so convincingly. Certainly far more convincingly than any sharp-suited pentest or red team consultant.
With dozens of fully accredited ethical hackers across the globe, and from all walks of life, we deliver simulated social engineering attacks in many languages, taking into account cultural differences.
The fine art of deception
Social engineering attacks can take many forms. And our expert team is well versed in all of them, bringing into play a hugely diverse set of skills to subvert their targets’ better judgment.
Their collective expertise has helped us become one of the few cyber vendors in the world fully accredited by CREST (Council for Registered Ethical Security Testers) for Simulated Targeted Attack and Response.
Constant cyber attack via subscription
For a simple monthly fee, our dedicated team of ethical hackers will constantly attack the full scope of your brand using digital, physical and social methods.
And when we find a way to breach your organization, we’ll raise the alarm before a real threat succeeds.

Collective
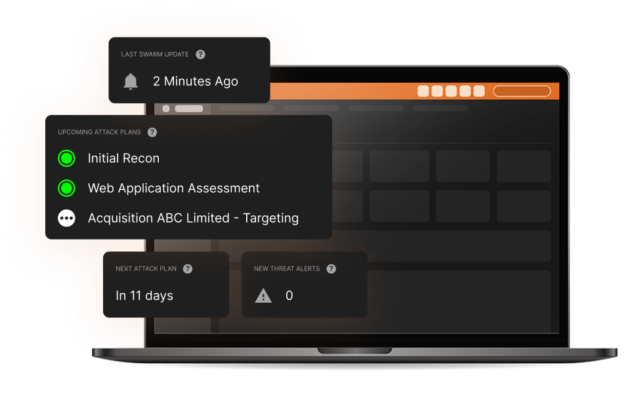
intelligence
The collective hive mind of our Swarm of ethical hackers is incorporated into our unique CovertSwarm Portal which can, in real time, direct our Swarm to any suspected weak areas of your business. It’s what enables us to put the ‘constant’ into ‘constant cyber attack’.
For you, a subscription will deliver significant value via long-term insights and instant access to our groundbreaking attack surface management portal, backed by our team of ethical hackers who are all fully employed by us.
REAL ATTACKERS DON’T REST. neither do we.
Cyber attacks are a constant threat. This is why testing on a six or twelve month cycle is no longer enough. Our subscription-based approach means the value delivered by our constant red team assault on your organization will be non-stop.
Via our CovertSwarm Portal you’ll have complete control over which areas of your business are attacked. We’ll respect boundaries and never place your systems in any genuine danger. But, just like a real attacker, we can’t promise we’ll always play by the traditional rules of testing.
CovertSwarm subscription includes:
- Constant cyber attack insights delivery
- Access to the CovertSwarm Portal
- Monthly ethical hacker time
- Dedicated account management via a senior CovertSwarm ethical hacker

The value of confidence
Starting from less than the cost of a single internal security hire, we have cybersecurity solutions for companies of all sizes, from SMEs up to enterprises, including discounted rates for public institutions, charities and B Corps.
Insights from the SWArm mind
Radical thinking and constant research inform all we do. Think ahead with shared intelligence from the CovertSwarm experts.

Sunday Times Best Places to Work. Three Years Running.
We attack businesses for a living. So we hold ourselves to the same standard internally. Here’s what 100% participation and three consecutive years in the Sunday…

DORA is not GDPR. Stop treating it like it is.
Most firms are treating DORA like GDPR: get a consultant, document the framework, move on. That worked for data privacy. It won’t work for a regulation…

Frontier AI models are exciting.
CovertSwarm COO Luke Potter on why frontier AI is genuinely exciting, why most of the conversation is asking the wrong questions, and what it means for…
Our services
Successful organizations are constant targets for malicious actors. Those who take security seriously don’t test their defenses once a year, they subscribe to CovertSwarm to attack continuously through our services.
- Breach and Attack Simulation Services
- Physical Cyber Attack Services
- Attack Surface Management Portal
- Red Team Services
- Penetration Testing Services
- Ethical Hacking Services
- Vulnerability Scanning
- Web Application Testing
- Ransomware Attack Simulation
- Phishing Attack Simulation
- Insider Threat Detection
- Password Strength Testing
- IT Infrastructure Testing



