Breach and Attack Simulation Services
Using occasional and limited scope pentesting as a defense is no defense at all. So let our expert red team of ethical hackers regularly expose the flaws in your systems through our breach and attack simulation (BAS) services. All well before your latest vulnerabilities are exploited by real threat actors.
The benefits of attack
Penetration testing is most effective when delivered in step with technology change. Not once a year, or only to a limited scope. Delivered on a recurring basis, it becomes a key element of a modern, multifaceted approach to your cyber security.
Don’t compromise. Don’t put your faith in an outmoded snapshot approach with limited scope and depth.
With CovertSwarm’s lifelike breach and attack simulation services, you will secure genuine value and new and unparalleled levels of cybersecurity.
- Certified ethical hackers
- Genuine cyber attack simulations
- Broader testing scopes
- Regular testing options
- A reduction in reporting noise
- Multi-disciplinary attack skill sets
- Real-time attack communication
- Risk remediation support
Rules of engagement
Just like your genuine worst cyber nightmare attackers, we don’t play by the rules. Certainly not those of the shiny-suited old world of pentest consultancy.
But there’s one rule we always comply with and that’s the mutually-agreed one which defines the circumstances, conditions and degree in which we launch our simulated cyber breaches and attacks on your organization. And that rule is to never putting your systems at genuine risk of harm.
Work with the best in the world
Our breach and attack simulation (BAS) services are delivered by our fully-employed and vetted Swarm of ethical hackers (not a marketplace) who are skilled at bringing to light previously undetected risks which will lead to security breaches and cyber attacks.
The collective expertise of our elite group has helped us become one of the few cyber vendors in the world fully accredited by the Council for Registered Ethical Security Testers (CREST) for Simulated Targeted Attack and Response.

Outpace your genuine cyber threats
Technology moves fast. And bad actors even faster. So the ‘snapshot’ delivered by conventional pentesting is out of date even before it hits your inbox.
Through our one-off and subscription approaches to testing, the relationships we build with your team, and the way we operate, avoids the risks and false economy of more generic testing. Our expert team working on your account will get to know your business, your people and the technologies that drive your competitive advantage. That’s context-aware testing.
The threat of cyber attack is constant. So are we.
You deserve to know when breach points appear in your organization’s constantly-evolving attack surface. The only way to achieve this is with a bad actor’s view. Which is where we come in.
Constant cyber attack subscription
Our Constant Cyber Attack Subscription delivers relentless, full-spectrum assaults across your digital, physical, and social surfaces.
Forget rigid scopes and waiting weeks for a report. We give you a relentless adversary, attacking, probing, and exposing weaknesses before real attackers do. And if we can’t break in, you’ll know your security investments are working.
Schedule a call with our team to discuss how we can help outpace cyber threats.

STOP TESTING. START ATTACKING.
Just as your security defenses must evolve to keep pace with organizational change, so must your approach to cyber attack.
With most security breaches occurring many days prior to detection, effective simulated attacks must be constant. It’s the only way to counteract an APT and avoid zero-day exploits.

NO PATCH FOR HUMAN ERROR
It’s not just your systems and applications which are susceptible to threat. Your people are too. Staff members are one of the most common breach points for successful cyber attacks.
That’s why, thinking beyond the digital, we’ll seek to exploit previous unexplored weaknesses in your physical and social environments too.
Collective
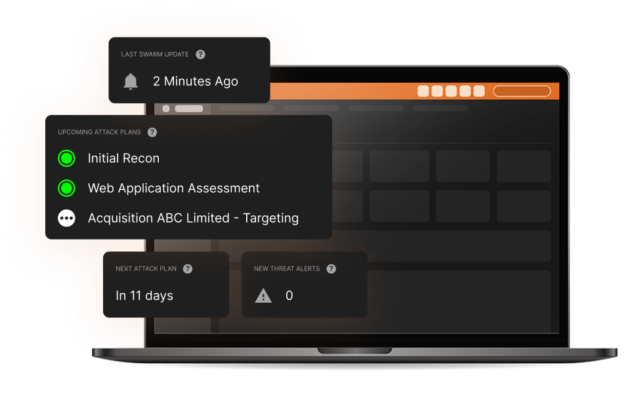
intelligence
The collective hive mind of our Swarm of ethical hackers is incorporated into our unique CovertSwarm Portal which can, in real time, direct our Swarm to any suspected weak areas of your business. It’s what enables us to put the ‘constant’ into ‘constant cyber attack’.
For you, a subscription will deliver significant value via long-term insights and instant access to our groundbreaking attack surface management portal, backed by our team of ethical hackers who are all fully employed by us.
REAL ATTACKERS DON’T REST. neither do we.
Cyber attacks are a constant threat. This is why testing on a six or twelve month cycle is no longer enough. Our subscription-based approach means the value delivered by our constant red team assault on your organization will be non-stop.
Via our CovertSwarm Portal you’ll have complete control over which areas of your business are attacked. We’ll respect boundaries and never place your systems in any genuine danger. But, just like a real attacker, we can’t promise we’ll always play by the traditional rules of testing.
CovertSwarm subscription includes:
- Constant cyber attack insights delivery
- Access to the CovertSwarm Portal
- Monthly ethical hacker time
- Dedicated account management via a senior CovertSwarm ethical hacker

The value of confidence
Starting from less than the cost of a single internal security hire, we have cybersecurity solutions for companies of all sizes, from SMEs up to enterprises, including discounted rates for public institutions, charities and B Corps.
Insights from the SWArm mind
Radical thinking and constant research inform all we do. Think ahead with shared intelligence from the CovertSwarm experts.

Proving Resilience: The Role of Regulator-Led Testing in Strengthening Market Stability.
How regulator-led testing fortifies market stability and sets a national standard Cyber threats are constantly evolving, with organizations facing sophisticated and persistent campaigns orchestrated by well-resourced…

The Evolution of EDR Bypasses: A Historical Timeline
The relationship between Endpoint Detection and Response (EDR) solutions and bypass techniques represents one of cybersecurity’s most dynamic battlegrounds. They are a representation of Cybersecurity as…

Billy Giles joins CovertSwarm as Head of Adversary Simulation for North America
CovertSwarm proudly welcomes Billy Giles as Head of Adversary Simulation for the North America region, strengthening our offensive cybersecurity capabilities and constant cyber attack subscription services.…
Our services
Successful organizations are constant targets for malicious actors. Those who take security seriously don’t test their defenses once a year, they subscribe to CovertSwarm to attack continuously through our services.
- Physical Cyber Attack Services
- Attack Surface Management Portal
- Social Engineering Services
- Red Team Services
- Penetration Testing Services
- Ethical Hacking Services
- Vulnerability Scanning
- Web Application Testing
- Ransomware Attack Simulation
- Phishing Attack Simulation
- Insider Threat Detection
- Password Strength Testing
- IT Infrastructure Testing



