Swarm Intelligence
A quiet finding with real-world impact. CVE-2026-33145 shows how xrdp's AlternateShell feature, enabled by default, passes client-supplied input directly into a shell, turning an RDP login into a clean, automatable command execution primitive.

When “Just Logging In” Isn’t Just Logging In: A Lookat xrdp and CVE-2026-33145
A quiet finding with real-world impact. CVE-2026-33145 shows how xrdp's AlternateShell feature, enabled by default, passes client-supplied input directly into…

Project Glasswing is impressive. But what about the rest?
Anthropic's Project Glasswing is a serious step forward for technical security. But it covers one third of the attack surface.…

Swarm Intelligence: Stryker’s Intune wipe proves your BCDR plan has a single point of failure
No malware. No ransomware. One compromised Global Admin account and the management console your IT team used this morning. The…

Claude Jailbroken To Attack Mexican Government Agencies
A threat actor jailbroke Claude to orchestrate a month-long attack on Mexican government networks, stealing 150 GB of sensitive data.…
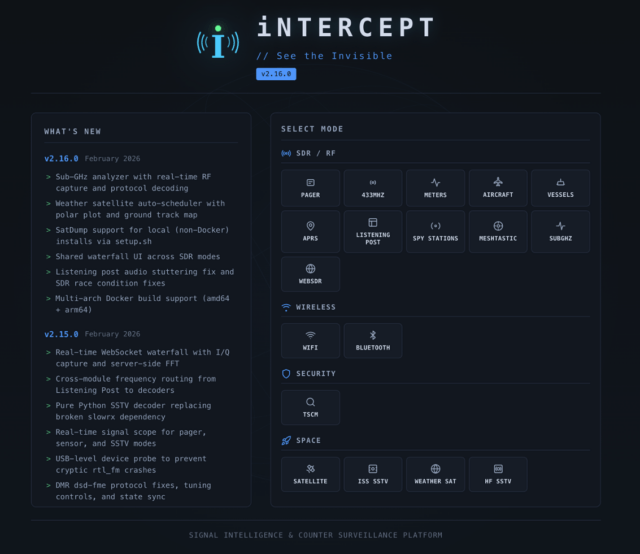
iNTERCEPT – How A Small RF Experiment Turned Into A Community SIGINT Platform
I've always been fascinated by RF. There's something about the fact that it's invisible, the fact that you might be…

When Your IDE Becomes An Insider: Testing Agentic Dev Tools Against Indirect Prompt Injection
Agentic development tools don't need to bypass your firewall. They're already inside. And if an attacker can control what they…

What Moltbook reveals about AI agent security
The Moltbook launch exposed a critical gap: organizations deploying AI agents faster than they can secure them. Research shows 22%…
Inject one agent, own them all: The cascading risk of multi-agent AI
Ninety percent of organizations are deploying AI agents. Most aren't monitoring what they do. Multi-agent systems amplify this blindspot: one…

Atlas AI: Local LLM inside Burp Suite
Atlas AI adds LLM-powered analysis to Burp Suite without sending data to the cloud. Built for offensive security teams who…