Resources
Radical thinking and constant research inform all we do. Think ahead with shared intelligence from our Swarm of ethical hackers.


Swarm Intelligence: LiteLLM was the end of the chain, not the beginning.
LiteLLM's PyPI package was backdoored for under an hour on March 24. SSH keys, cloud credentials, and CI/CD secrets exfiltrated…
Handala & MuddyWater: MDM Weaponization at Enterprise Scale
On 11 March 2026, an Iranian two-team operation destroyed 200,000 enterprise devices at Stryker without deploying a single piece of…

Why Robbing Banks Is Easy (And Why That Should Terrify You)
A globally recognized ethical hacker shares real social engineering stories from legally robbing banks across five continents. The tools change.…

Swarm Intelligence: Stryker’s Intune wipe proves your BCDR plan has a single point of failure
No malware. No ransomware. One compromised Global Admin account and the management console your IT team used this morning. The…

Dynamic Attack Surfaces: The Professional Sports Problem
Professional sports organizations face cybersecurity challenges that don't fit traditional frameworks. With seasonal spikes, constant third-party integrations, and workforce volatility,…

Claude Jailbroken To Attack Mexican Government Agencies
A threat actor jailbroke Claude to orchestrate a month-long attack on Mexican government networks, stealing 150 GB of sensitive data.…

Jayson E Street Joins CovertSwarm
The man who accidentally robbed the wrong bank in Beirut is now part of the Swarm. Jayson E Street joins…
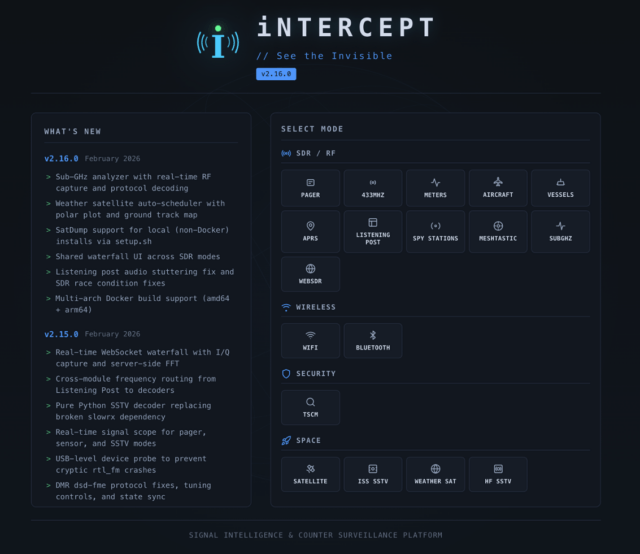
iNTERCEPT – How A Small RF Experiment Turned Into A Community SIGINT Platform
I've always been fascinated by RF. There's something about the fact that it's invisible, the fact that you might be…

When Your IDE Becomes An Insider: Testing Agentic Dev Tools Against Indirect Prompt Injection
Agentic development tools don't need to bypass your firewall. They're already inside. And if an attacker can control what they…