Resources
Radical thinking and constant research inform all we do. Think ahead with shared intelligence from our Swarm of ethical hackers.


An In-Depth Guide to Remote Desktop Protocol (RDP)
The continually changing nature of today's workplace has made remote access technology essential.
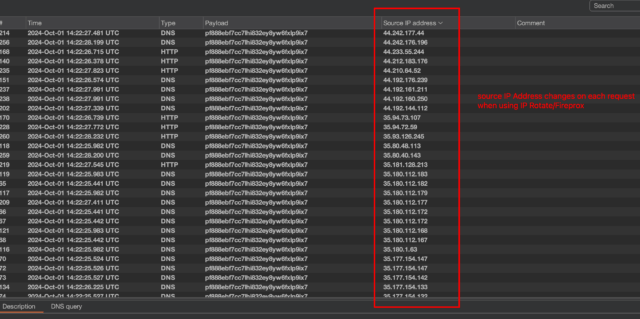
Mitigating Credential Stuffing Attacks with IP Rotation: Strategies and Considerations
This article covers effective strategies to fight credential-stuffing attacks using IP rotation. By Ibai Castells
CovertSwarm at DEF CON 32: Insights from the Swarm
This time last week, our Swarm was taking over Las Vegas at DEF CON 32 - one of the biggest…

How to Own DEF CON Like a Boss
The Swarm have landed in DEF CON, and we have some tips from our experts about surviving, and thriving, at…

Cybersecurity Glossary
Read this comprehensive list we've compiled to assist experts, C-level executives, and those embarking on a cybersecurity career in navigating…

DEF CON 32: Discover the New CovertSwarm Badge
With the badge life community stronger than ever, we're excited to announce our second CovertSwarm badge for DEF CON 32.
Academy Launches Second Intake
CovertSwarm's Academy is opening the 2024 intake. Apply and start your cybersecurity journey as an ethical hacker.

Combining regulation with real-world security assurance: DORA and NIS2
Whether you’re a local financial startup or a multinational food distributor, understanding how DORA and NIS2 may affect your organization…

CovertSwarm named by Clutch among Top 100 Fastest-Growing Companies
Clutch has recognized us for achieving one of the highest revenue growth rates from 2022 to 2023.