Resources
Radical thinking and constant research inform all we do. Think ahead with shared intelligence from our Swarm of ethical hackers.


K8s – Pod to Node Escape Techniques
In this article we are exploring the breakout of a pod, to gain access to a node. This is performed…

Rishikesh Bhide joins CovertSwarm as Head of Engineering
Rishikesh joins CovertSwarm to accelerate the organization’s engineering capabilities and product strategy as part of its rapid growth trajectory.

Louis Blackburn joins as Operations Director
Louis joins CovertSwarm from Lloyds Banking Group with an extensive background in red teaming, becoming the latest senior hire as…

CovertBrew February Edition
Our first ever CovertBrew networking event.
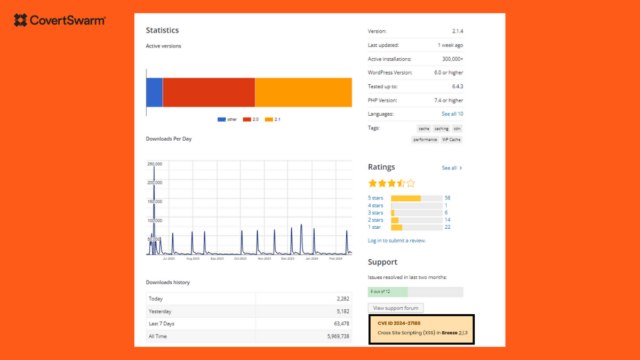
Discovering WordPress Vulnerabilities to Make it Safer
Breeze - WordPress Cache Plugin

Exploiting CVE-2023-5044 and CVE-2023-5043 to overtake a Kubernetes Cluster
In this blog we are exploring two new CVE's that exploit an issue in the NGINX controller when NGINX is…

Uncloaking Radio Frequency Identification (RFID)
Demystify RFID with insights on components, tag types, modulation, and use cases. A concise guide to the intricate world of…

A journey into Badge Life
Explore CovertSwarm's Badge Life journey from Defcon 30 chaos to Defcon 31 triumphs. Join the hardware hacking adventure in this…

Gaining Initial Access in a Kubernetes Environment (part 2)
Explore initial access in Kubernetes: Uncover application vulnerabilities, compromised images, and cloud credential misuse in Kubernetes environments.